Stay informed and never miss a Foolproof update!
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.
A paradigm shift is occurring due to increasing global policy regulating blockchain and digital assets. The blockchain industry faces a critical inflection point as regulatory frameworks like the Digital OperationalResilience Act (DORA) reshape the financial sector’s approach to technology risk. The reliance on third-party service providers creates significant vulnerabilities, while transitioning to robust middleware tooling offers a path to genuine security, compliance, and widespread adoption.
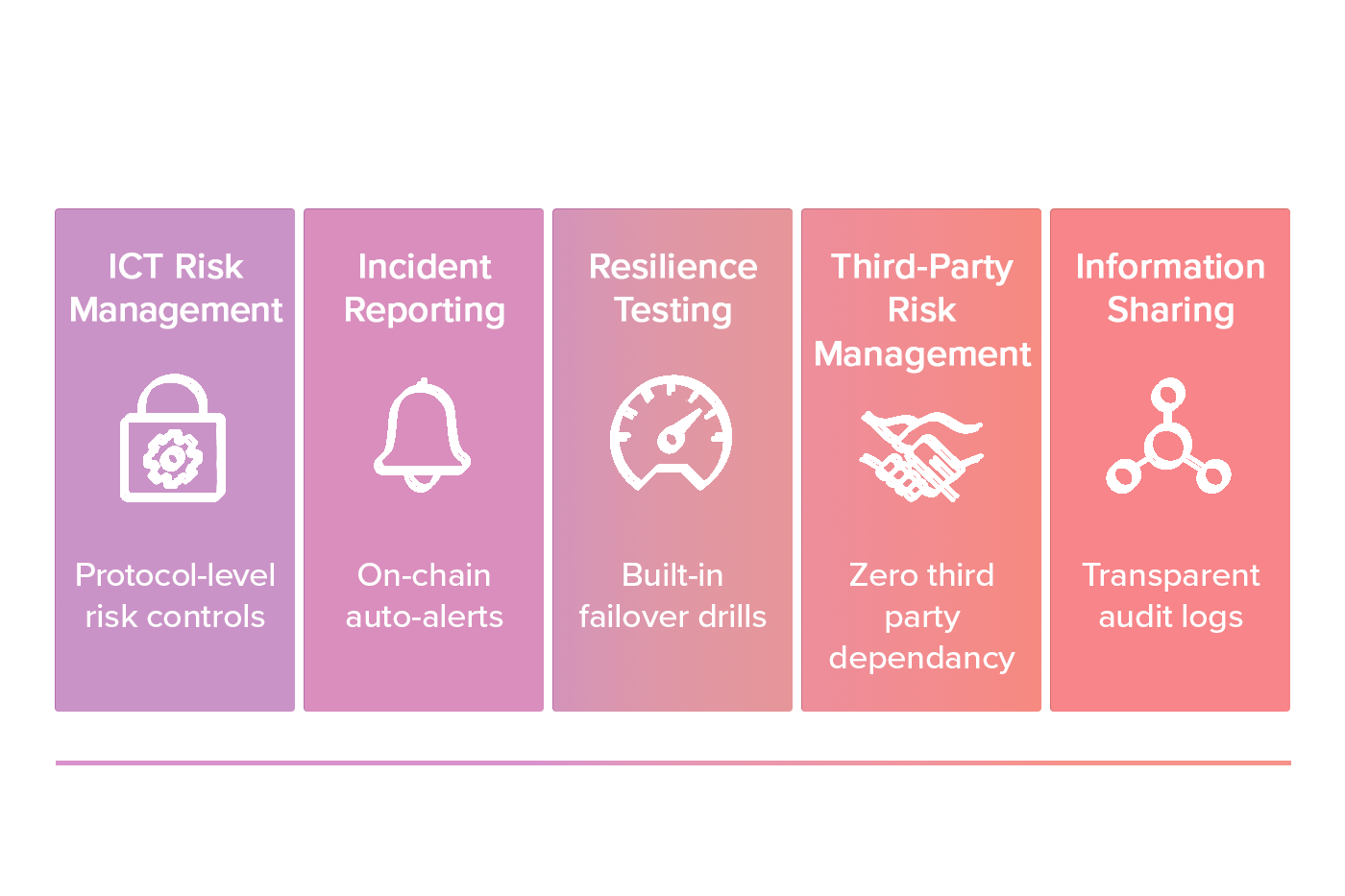
January 17, 2025, marked a watershed moment for financial institutions operating in the European Union. The Digital Operational Resilience Act (DORA)came into full force, establishing unprecedented requirements for operational resilience in the face of technological disruptions. DORA introduces uniform requirements across all EU member states, focusing on five key pillars:
For crypto asset service providers and financial institutions dealing with blockchain technology, DORA presents both challenges and opportunities.The regulation covers an unprecedented scope of financial entities, from traditional banks to cryptocurrency exchanges and trading platforms, imposing stringent requirements to ensure operational stability.
While third-party service providers like Fireblocks, BitGo, and Coinbase Custody have emerged as vital infrastructure in the crypto ecosystem, the current landscape presents significant security and operational challenges.

As outlined in Foolproof’s “Making Blockchain Foolproof” paper, today’s institutional custody landscape forces an impossible choice between security and control:
Security at the Cost of Control: Traditional custodial services offer institutional-grade security but impose significant limitations:
Control at the Cost of Security: Self-custody solutions provide complete control but introduce different challenges:
DORA specifically addresses the risks of third-party dependence, recognizing that financial entities often rely on external service providers for critical ICT functions. The regulation demands rigorous assessment and management of these relationships, placing the full burden of responsibility on the financial entities themselves.
Under DORA, financial institutions must:
While many service providers like Fireblocks are adapting their offerings to help clients meet these requirements, the fundamental issue remains: reliance on third-party middlemen creates inherent vulnerabilities that contradict the decentralized ethos of blockchain technology.
The answer to these challenges doesn’t lie in more sophisticated third-party services, but in a fundamental architectural shift toward blockchain-native middleware tools. This approach, championed by Foolproof and increasingly recognized throughout the industry, represents a paradigm change in how we approach blockchain security and management.
Foolproof’s pioneering, patented middleware approach leverages blockchain’s inherent capabilities to create management systems that feel natural to users while maintaining security and decentralization:
Core Blockchain Capabilities:
The transition from middlemen service providers to middleware tooling offers several critical advantages that directly address DORA compliance challenges:
1. Reduced Counterparty Risk: Unlike third-party custodians, middleware tools allow users to avoid taking custody of assets. Instead, they provide the infrastructure for users to maintain control while implementing sophisticated security measures. This significantly reduces the counterparty risk that DORA aims to mitigate.
2. Enhanced Operational Resilience:Middleware tools create inherently resilient systems by building security into the blockchain rather than relying on external services. This aligns perfectly with DORA’s emphasis on operational continuity during disruptions.
3. Transparent Risk Management: Middleware solutions provide clear visibility into the security measures and controls being implemented, making it easier for financial institutions to demonstrate compliance with DORA’s risk management requirements.
4. Seamless Exit Strategies: With middleware tools, financial institutions aren’t locked into specific service providers; The ability to maintain control while leveraging enhanced security features addresses DORA’s emphasis on exit planning.
5. Distributed Security Model: Rather than centralizing security with a single provider (creating a potential single point of failure), middleware distributes security across the blockchain, creating amore resilient system overall.
Foolproof’s patented approach demonstrates how middleware tools can transform several critical areas of blockchain interaction:
Foolproof’s middleware architecture introduces a revolutionary approach to custody:
Key Architectural Innovations:
This architecture enables sophisticated institutional applications, including treasury management, trading desk operations, client asset management, and regulatory compliance.
For liquid staking derivatives, a rapidly growing sector in the blockchain ecosystem, middleware tools address critical vulnerabilities:
Current Liquid Staking Limitations:
Foolproof’s Technical Innovation:
Liquidity pools, fundamental to DeFi infrastructure, also benefit significantly from middleware security:
Critical Security Vulnerabilities in Current LP Tokens:
Foolproof’s Technical Approach:
Financial institutions seeking to comply with DORA while maintaining the benefits of blockchain technology should consider a strategic shift toward middleware tooling. This approach offers several advantages specific to DORA compliance:
1. Improved ICT Risk Management:
2. Enhanced Incident Response:
3. Simplified Third-Party Risk Management:
4. Future-Proof Compliance:
For financial institutions looking to make the shift from third-party service providers to middleware tooling, a phased approach can minimize disruption:
1. Assessment:
2. Pilot Implementation:
3. Gradual Transition:
4. Comprehensive Training:
5. Continuous Evaluation:
The implementation of DORA represents both a challenge and an opportunity for the blockchain industry. By forcing financial institutions to reconsider their approach to digital operational resilience, the regulation creates an impetus for fundamental innovation.
The transition from middlemen service providers to middleware tooling aligns perfectly with this moment of regulatory evolution. By building security and management capabilities directly into blockchain systems, we can create more compliant solutions that align with blockchain technology’s decentralized ethos.
Foolproof’s pioneering work demonstrates that blockchain-native middleware is not merely theoretical; it represents a practical path forward for institutions seeking to navigate the complex regulatory compliance landscape while maintaining the security and flexibility needed for effective digital asset management.
As the industry matures, organizations embracing middleware tooling will find themselves better positioned to comply with DORA and other emerging regulations, like GENIUS, while delivering the security and control clients increasingly demand. The future of blockchain security lies not in more sophisticated middlemen but in smarter, more capable middleware that leverages the technology’s unique capabilities.
Chain alysis. (2025, February). 2025 Crypto Crime Report:
Introduction. https://www.chainalysis.com/blog/2025-crypto-crime-report-introduction/
European Banking Authority. (2025, January). Digital Operational Resilience Act (DORA). https://www.eiopa.europa.eu/digital-operational-resilience-act-dora_en
European Commission. (2023, January 16). Digital Operational Resilience Act: Regulation (EU) 2022/2554. Official Journal of the European Union. https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:32022R2554&from=FR
Fireblocks. (2025). Navigating DORA Compliance for Third-Party ICT Vendors: A CISO’s Guide with Fireblocks. https://www.fireblocks.com/resources/navigating-dora-compliance-for-third-party-ict-vendors/
Foolproof. (2025). Making Blockchain Foolproof: The Fundamental Challenge. Foolproof Technologies. https://github.com/fool-proof-labs/shadow-token/blob/main/README.md
Keepit. (2024, July 17). What is the EU Digital Operational Resilience Act (DORA)? https://www.keepit.com/blog/what-is-dora/
Lattice. (2024). The Middleware Thesis. https://lattice.mirror.xyz/30fvMb2MxoH2pRQ_5pXsGmudR62-RvrNKEzHluxYGrU
Mayer Brown. (2025, January 17). Cybersecurity in the Financial Sector: EU’s Digital Operational Resilience Act Takes Effect. https://www.mayerbrown.com/en/insights/publications/2025/01/cybersecurity-in-the-financial-sector-eus-digital-operational-resilience-act-takes-effect
PwC. (2023). Introducing the Digital Operational Resilience Act. https://www.pwc.com/mt/en/publications/technology/dora.html
Reuters. (2025, May 15). Coinbase says cyber criminals stole account data of some customers. https://www.reuters.com/business/coinbase-says-cyber-criminals-stole-account-data-some-customers-2025-05-15/
U.S. Congress. (2025). S.394 — A bill to establish requirements for certain cryptocurrency transactions, and for other purposes. Congress.gov. https://www.congress.gov/bill/119th-congress/senate-bill/394/text